Today, let’s embark on a journey of deploying Stan’s Robot Shop, an educational microservices application. This sandbox environment serves as an excellent playground to delve into the realm of containerized applications, exploring deployment methodologies in a practical manner.
COMPLETE CREDITS ABHISHEK VEERAMALLA
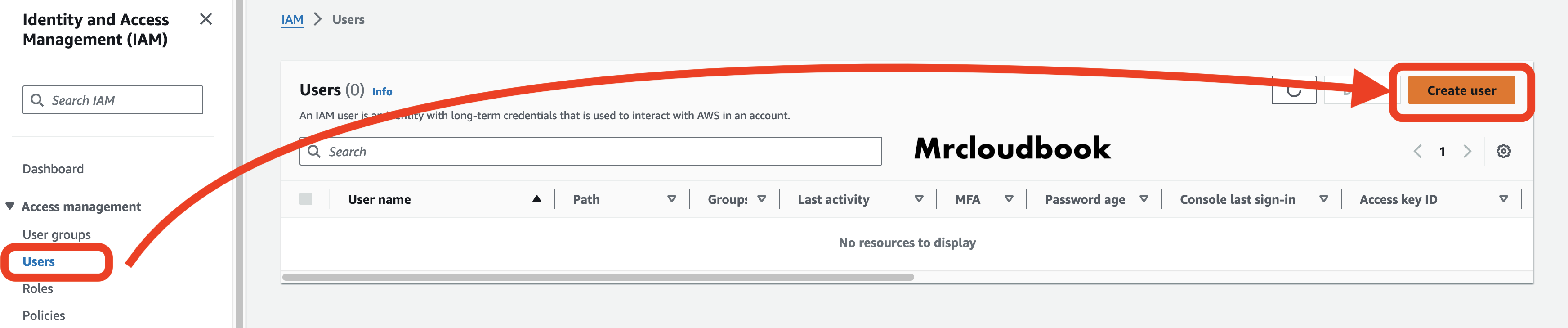
STEP1: CREATE IAM USER IN AWS
Go to Aws console and login with your credentials
IN Search bar TYPE IAM
This is IAM Dashboard
Click on Users and click on Create User
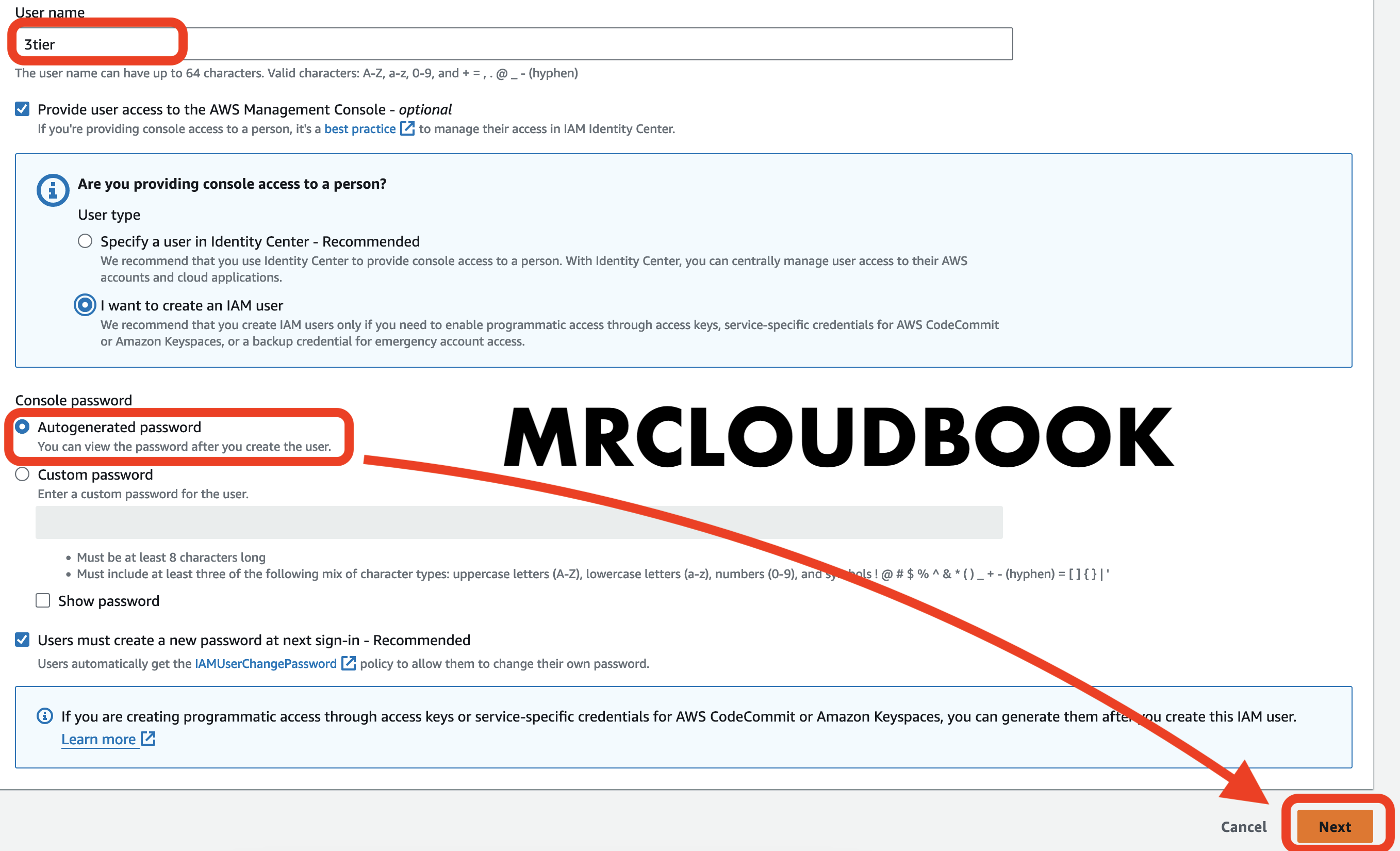
Provide a Name and provide checkboxes and click on Next
Click on Attach Policies directly
Use AdministratorAccess Just for learning purpose
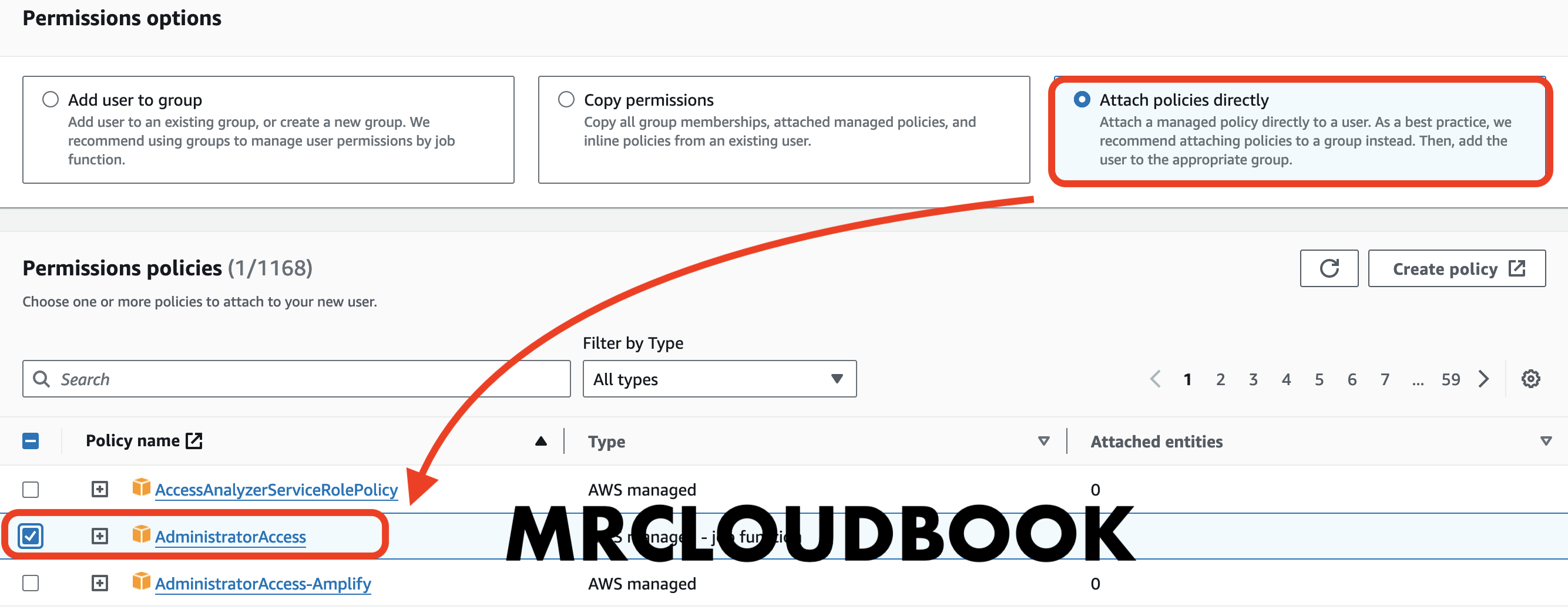
Click Next
Click on Create user

Click on View user
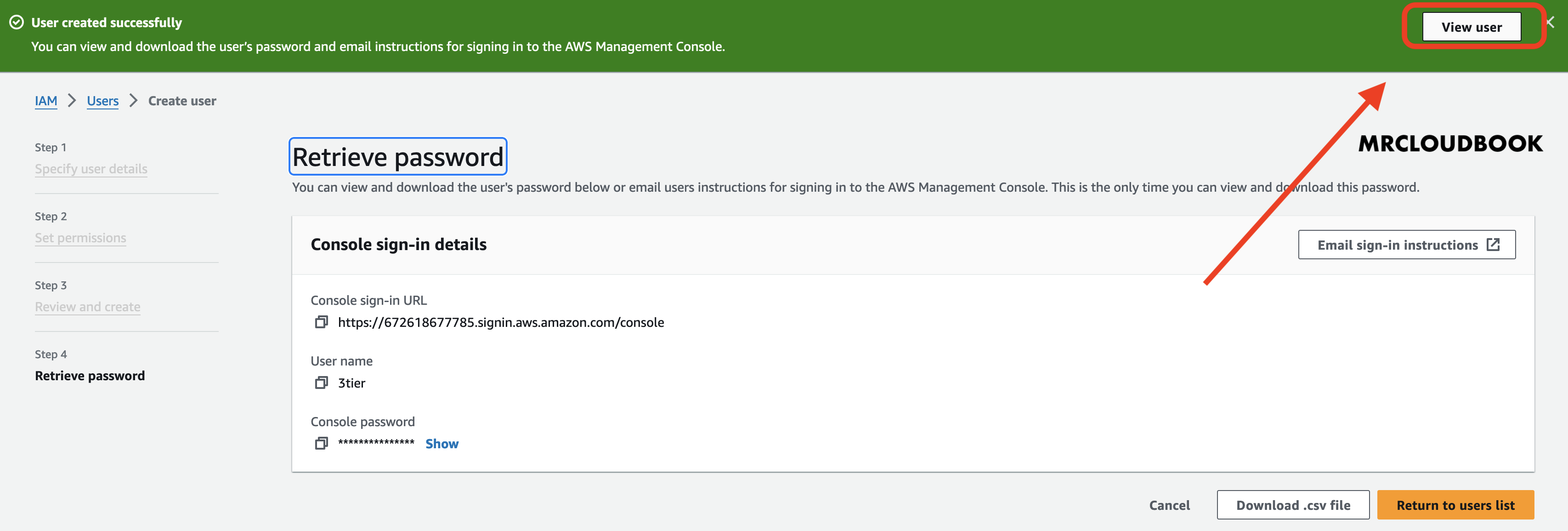
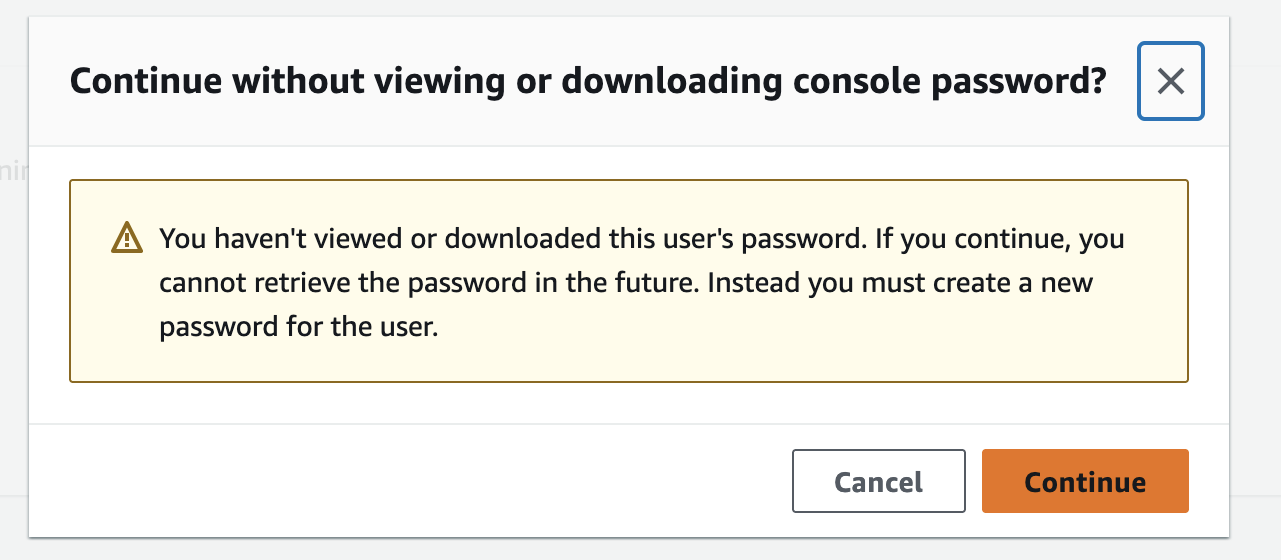
Click on Continue
Click on Security credentials
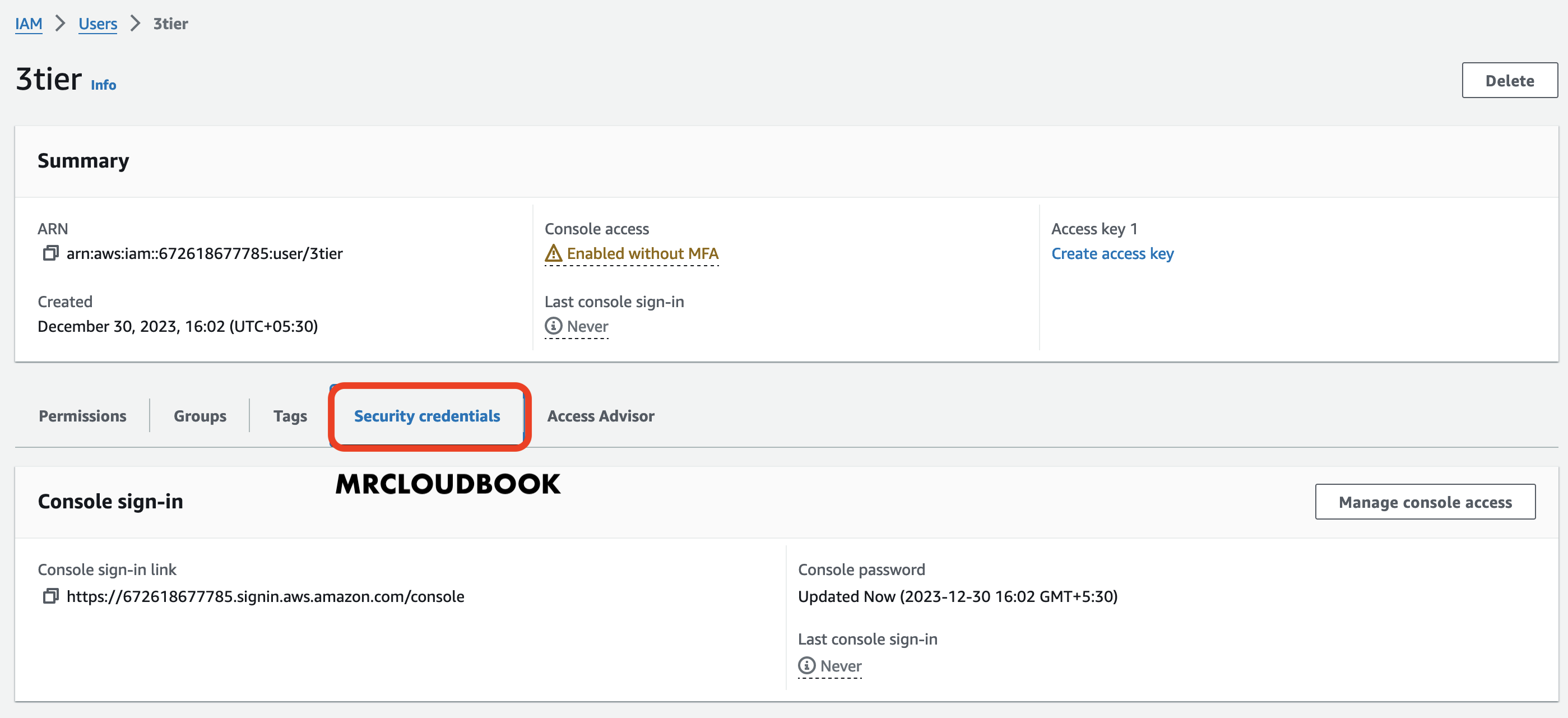
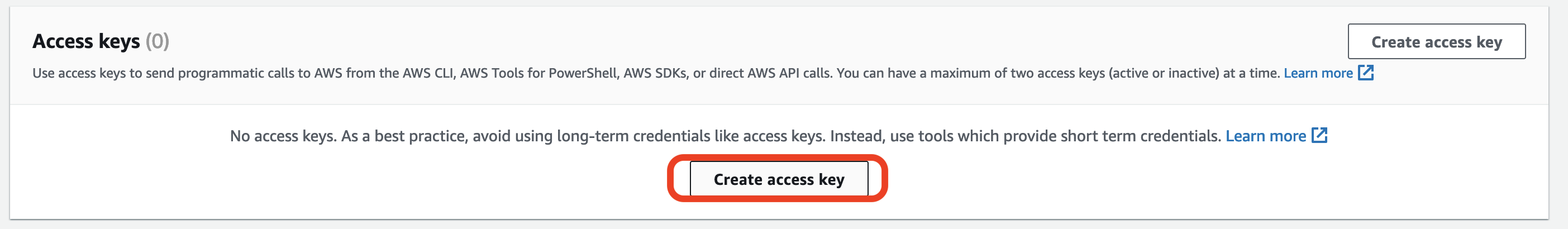
Now under security credentials, Go to Access keys
Click on Create access key
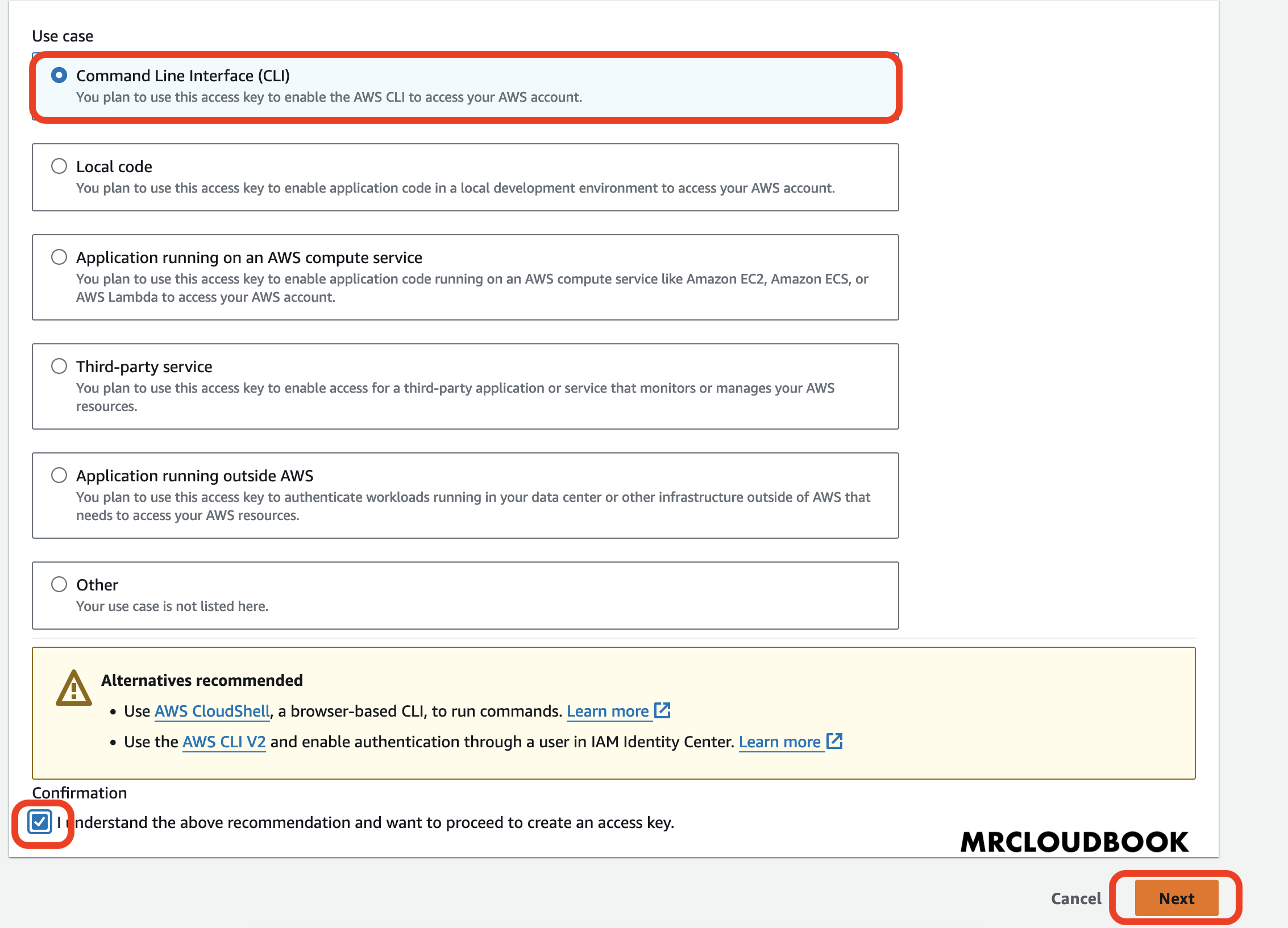
Select CLI & Accept terms and click on Next
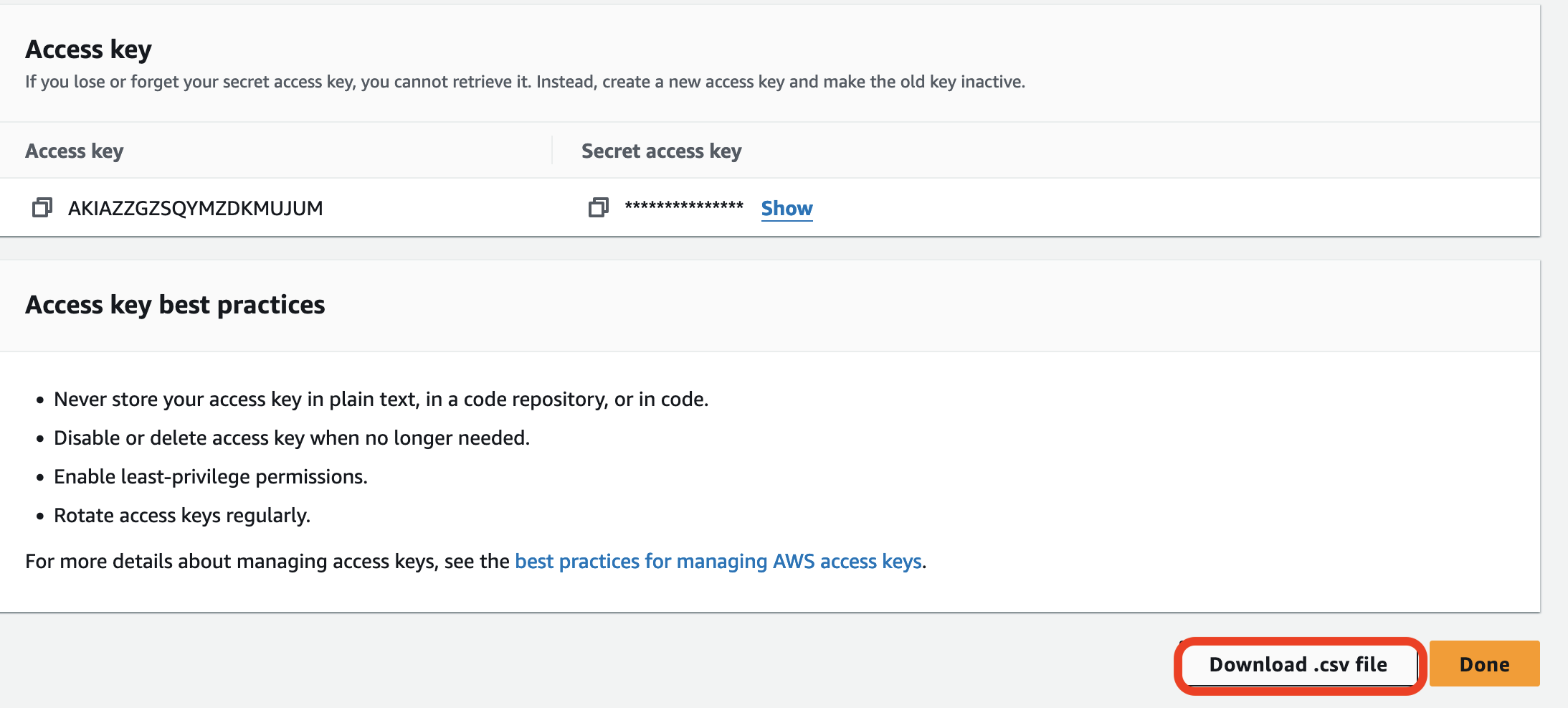
Download .csv file and click on Done
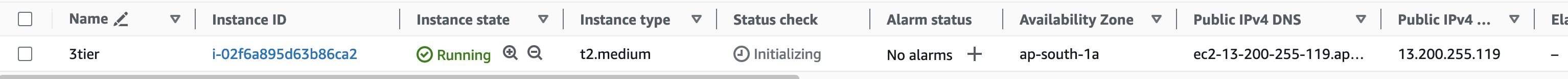
STEP2: Create EC2 Instance
- Sign in to AWS Console: Log in to your AWS Management Console.
- Navigate to EC2 Dashboard: Go to the EC2 Dashboard by selecting “Services” in the top menu and then choosing “EC2” under the Compute section.
- Launch Instance: Click on the “Launch Instance” button to start the instance creation process.
- Choose an Amazon Machine Image (AMI): Select an appropriate AMI for your instance. For example, you can choose Ubuntu image.
- Choose an Instance Type: In the “Choose Instance Type” step, select
t2.mediumas your instance type. Proceed by clicking “Next: Configure Instance Details.” - Configure Instance Details:
For “Number of Instances,” set it to 1 (unless you need multiple instances).
7. Configure additional settings like network, subnets, IAM role, etc., if necessary.
8. For “Storage,” click “Add New Volume” and set the size to 8GB (or modify the existing storage to 16GB).
9. Click “Next: Add Tags” when you’re done.
10. Add Tags (Optional): Add any desired tags to your instance. This step is optional, but it helps in organizing instances.
11. Configure Security Group:
Choose an existing security group or create a new one.
12. Ensure the security group has the necessary inbound/outbound rules to allow access as required.
13. Review and Launch: Review the configuration details. Ensure everything is set as desired.
14. Select Key Pair:
Select “Choose an existing key pair” and choose the key pair from the dropdown.
15. Acknowledge that you have access to the selected private key file.
16. Click “Launch Instances” to create the instance.
17. Access the EC2 Instance: Once the instance is launched, you can access it using the key pair and the instance’s public IP or DNS.
Ensure you have necessary permissions and follow best practices while configuring security groups and key pairs to maintain security for your EC2 instance.
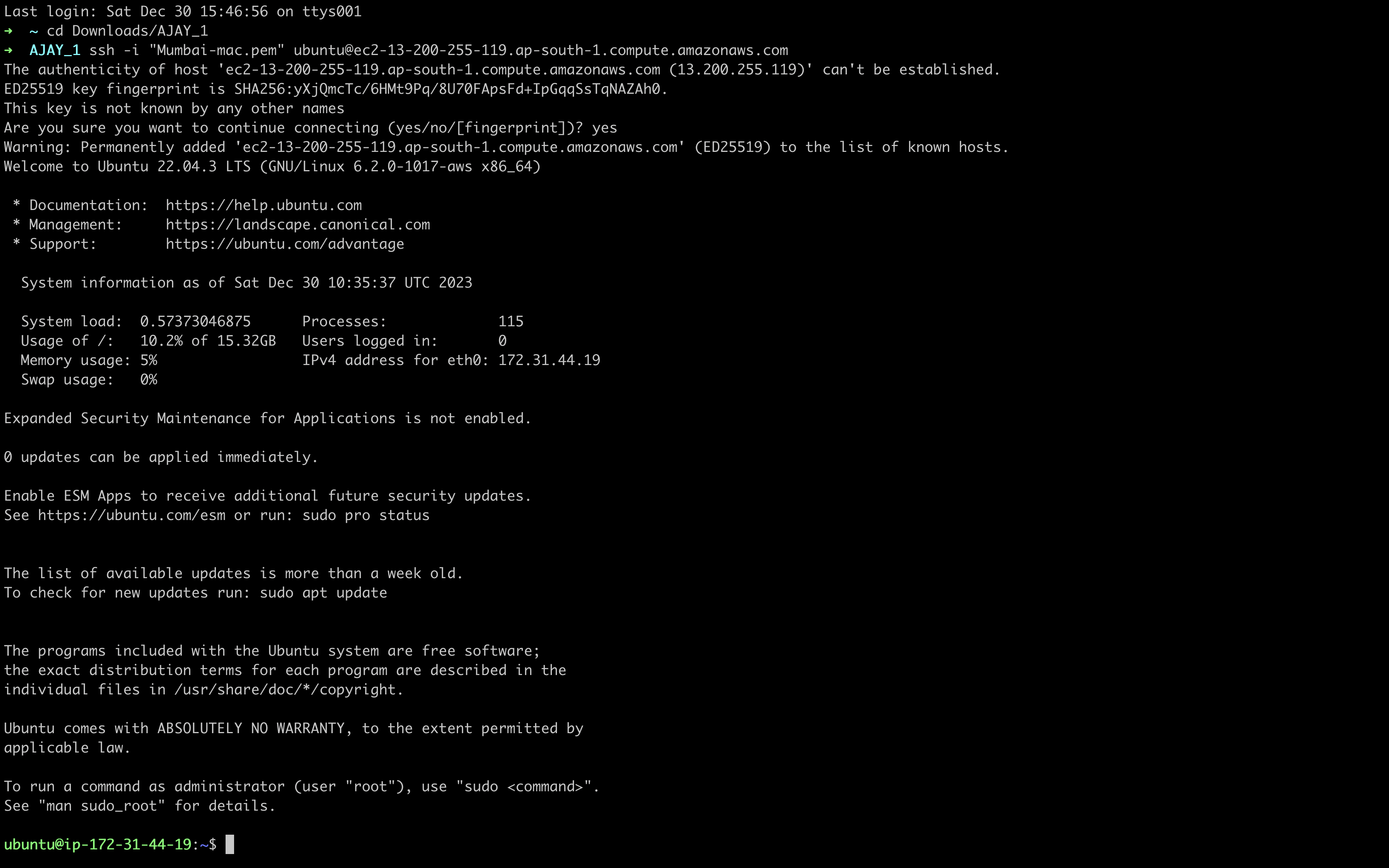
Step3: Connect to Instance and Install Required Packages
Eksctl
sudo apt update
curl --silent --location "https://github.com/weaveworks/eksctl/releases/latest/download/eksctl_$(uname -s)_amd64.tar.gz" | tar xz -C /tmp
sudo mv /tmp/eksctl /usr/local/bin
eksctl version

Kubectl
curl -O https://s3.us-west-2.amazonaws.com/amazon-eks/1.28.3/2023-11-14/bin/linux/amd64/kubectl
chmod +x ./kubectl
mkdir -p $HOME/bin && cp ./kubectl $HOME/bin/kubectl && export PATH=$HOME/bin:$PATH
kubectl version --client


Aws CLI
sudo apt install unzip -y
curl "https://awscli.amazonaws.com/awscli-exe-linux-x86_64.zip" -o "awscliv2.zip"
unzip awscliv2.zip
sudo ./aws/install


Helm
curl -fsSL -o get_helm.sh https://raw.githubusercontent.com/helm/helm/main/scripts/get-helm-3
chmod 700 get_helm.sh
./get_helm.sh

STEP4: EKS Setup
Aws configure ( Use us-east-1 region please )
aws configure

Lets clone GitHub repo
git clone https://github.com/Aj7Ay/3Tier-Robot-shop.git
cd 3Tier-Robot-shop

Create cluster
eksctl create cluster --name demo-cluster-three-tier-1 --region us-east-1

Now Setup
Commands to configure IAM OIDC provider
USE CLUSTER NAME demo-cluster-three-tier-1
export cluster_name=
The command “export cluster_name=” is used in a computer’s command-line interface to create a named storage space (variable) that holds a specific value. It’s like giving a name to something so you can use it later. In this case, it’s creating a storage space called “cluster_name” and putting a value in it, which represents the name of a cluster. This helps remember and use the cluster’s name in other commands or programs without typing it repeatedly.
oidc_id=$(aws eks describe-cluster --name $cluster_name --query "cluster.identity.oidc.issuer" --output text | cut -d '/' -f 5)
This command uses the AWS CLI (Command Line Interface) to extract a specific piece of information about an Amazon EKS (Elastic Kubernetes Service) cluster
Check if there is an IAM OIDC provider configured already
aws iam list-open-id-connect-providers | grep $oidc_id | cut -d "/" -f4
This command utilizes the AWS CLI (Command Line Interface) to list OpenID Connect (OIDC) providers in your AWS Identity and Access Management (IAM) and extract specific information
eksctl utils associate-iam-oidc-provider --cluster $cluster_name --approve
EKSCTL command used to associate the IAM OIDC provider with an Amazon EKS (Elastic Kubernetes Service) cluster.

Setup alb add on
Download IAM policy
curl -O https://raw.githubusercontent.com/kubernetes-sigs/aws-load-balancer-controller/v2.5.4/docs/install/iam_policy.json

Create IAM Policy
aws iam create-policy \
--policy-name AWSLoadBalancerControllerIAMPolicy \
--policy-document file://iam_policy.json

create IAM role
Please Add cluster name and Aws account ID
eksctl create iamserviceaccount \
--cluster= \
--namespace=kube-system \
--name=aws-load-balancer-controller \
--role-name AmazonEKSLoadBalancerControllerRole \
--attach-policy-arn=arn:aws:iam:::policy/AWSLoadBalancerControllerIAMPolicy \
--approve
To get aws account id
Go to aws console and click on Right side profile name and copy it


Deploy ALB controller
Add helm repo
helm repo add eks https://aws.github.io/eks-charts
Update the repo
helm repo update eks

Install
please update VPC_ID in this command
go to eks and copy vpc id

helm install aws-load-balancer-controller eks/aws-load-balancer-controller -n kube-system --set clusterName=demo-cluster-three-tier-1 --set serviceAccount.create=false --set serviceAccount.name=aws-load-balancer-controller --set region=us-east-1 --set vpcId=

Verify that the deployments are running
kubectl get deployment -n kube-system aws-load-balancer-controller

EBS CSI Plugin configuration
The Amazon EBS CSI plugin requires IAM permissions to make calls to AWS APIs on your behalf.
Create an IAM role and attach a policy. AWS maintains an AWS managed policy or you can create your own custom policy. You can create an IAM role and attach the AWS managed policy with the following command. Replace my-cluster with the name of your cluster. The command deploys an AWS CloudFormation stack that creates an IAM role and attaches the IAM policy to it.
Please add Cluster name
eksctl create iamserviceaccount \
--name ebs-csi-controller-sa \
--namespace kube-system \
--cluster \
--role-name AmazonEKS_EBS_CSI_DriverRole \
--role-only \
--attach-policy-arn arn:aws:iam::aws:policy/service-role/AmazonEBSCSIDriverPolicy \
--approve

Run the following command. Replace with the name of your cluster, with your account ID.
eksctl create addon --name aws-ebs-csi-driver --cluster --service-account-role-arn arn:aws:iam:::role/AmazonEKS_EBS_CSI_DriverRole --force

Now Go inside the helm and create a namespace
cd helm
kubectl create ns robot-shop

Now
helm install robot-shop --namespace robot-shop .

Now check pods
kubectl get pods -n robot-shop

Check service
kubectl get svc -n robot-shop

Now Apply ingress
kubectl apply -f ingress.yaml

Now go to AWS CONSOLE
search for Ec2 and Go to load balancers
COPY DNS

Open a new tab and paste


STEP5: DELETE CLUSTER
JUST PROVIDE THIS COMMAND
eksctl delete cluster --name demo-cluster-three-tier-1 --region us-east-1

In conclusion, our journey through the deployment and configuration of Stan’s Robot Shop, a versatile microservices application, has been an enlightening exploration into the world of containerized applications, orchestration, and monitoring.
Throughout this guide, we’ve covered a range of essential steps, from deploying the application using Docker Compose to associating IAM OIDC providers with Amazon EKS clusters, unlocking the potential for secure access to AWS resources through Kubernetes service accounts.
Stan’s Robot Shop serves not only as a sandbox for experimenting with diverse technologies like NodeJS, Java, Python, and more but also as a practical learning ground for understanding orchestration tools like Kubernetes and monitoring solutions like Instana.
As you continue to delve into the intricacies of microservices architectures, container orchestration, and monitoring practices, remember that Stan’s Robot Shop is an ideal starting point-a playground where you can further explore, test, and refine your skills in a safe and controlled environment.
We hope this guide has provided valuable insights and practical guidance, empowering you to take your knowledge and understanding of containerized applications and Kubernetes to the next level.



Comments (9)
where is container & how it's achieving the CI process? if you can explain the flow it will be better. like, how to scale it with a container . inside it's repo there is one dockerfile for one microservice. how to use them etc etc. btw, thanks for your contribution.
Already i provided in link for the video in starting please watch if you have doubts
Hi There, I hope you're well! Your new website venture caught my eye, and I'm genuinely excited about its potential. As a WordPress expert passionate about creating impactful digital experiences, I see great opportunities to elevate your project. Could we schedule a quick chat to explore ideas? I'd love to share insights tailored to your goals. Let me know a time that suits you. Looking forward to the possibility of collaborating! Best, Mahmud Ghazni WordPress Expert Extraordinaire Email: ghazni@itsyourdev.com WhatsApp: https://wa.me/8801322311024
will think about it
can we make it to ci/cd setup and deploy it monitoring and checking alerts
but it will be lengthy you can try bro if you want
i followed the same process..why ingress file is not there in path ..is there any solution
ingress file is in /EKS/helm/ingress.yaml
why you change the dir while installng helm i didnt understand
Leave a comment