Who Is TeamPCP?
TeamPCP (also tracked as PCPcat, PersyPCP, ShellForce, and DeadCatx3) is a cloud-native cybercriminal operation that has been active since at least December 2025. They are not opportunistic script kiddies - they are a sophisticated, automated, multi-ecosystem threat actor with AI-assisted tooling, blockchain C2 infrastructure, and now an active collaboration with the LAPSUS$ extortion group.
Their Telegram channels (@Persy_PCP and @teampcp) show a group that taunts its victims directly. After compromising Checkmarx, they posted: "These companies were built to protect your supply chains yet they can't even protect their own, the state of modern security research is a joke." They embed TeamPCP Cloud stealer directly in their payload strings - they want to be known.
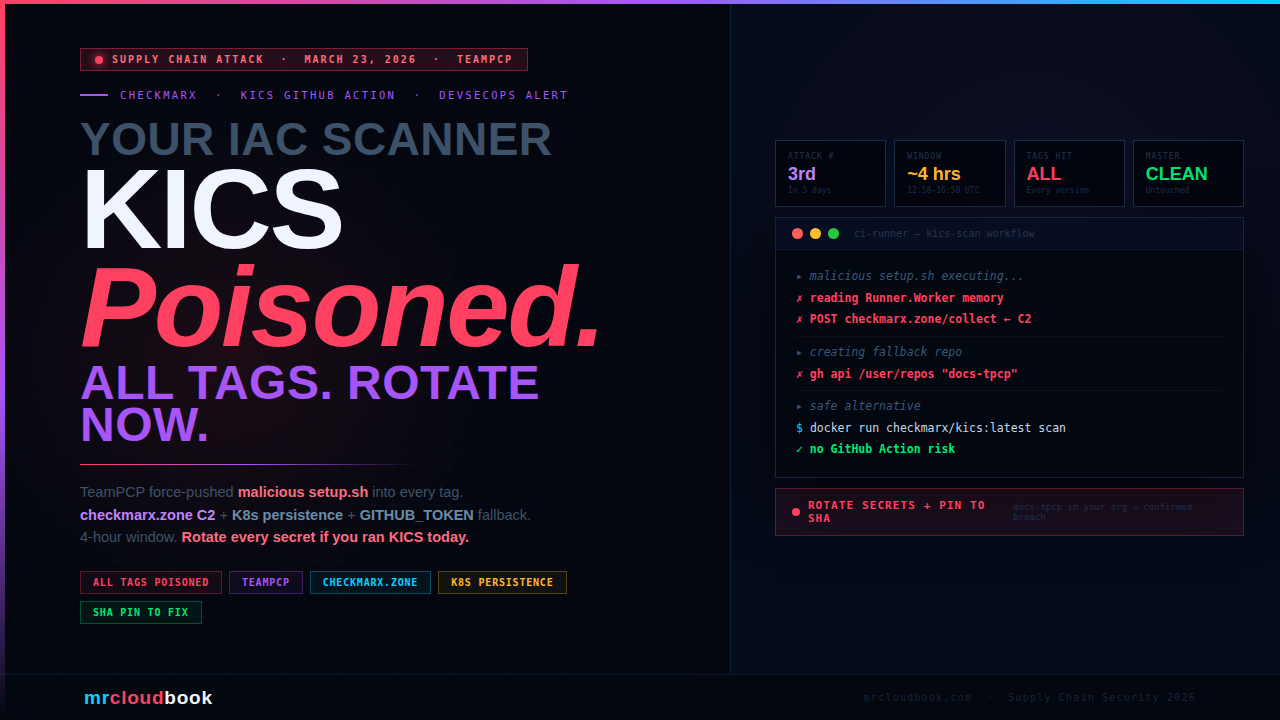
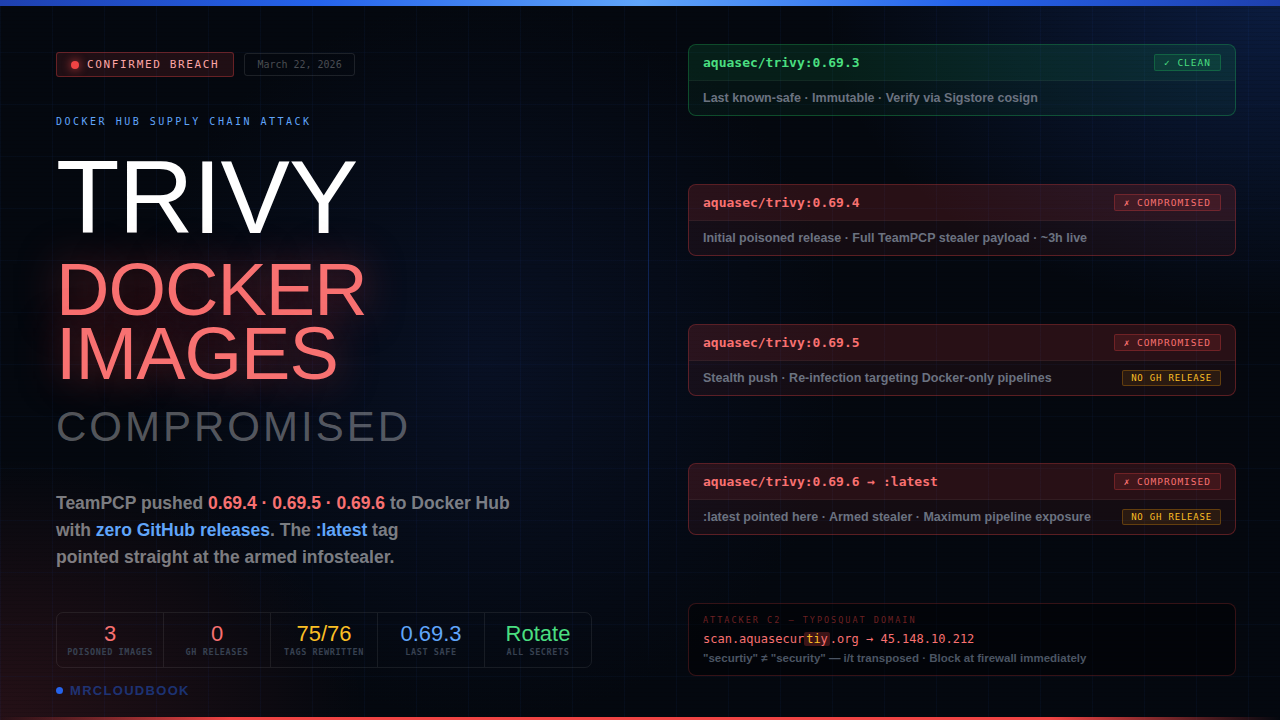
What makes TeamPCP especially dangerous is their operational model: every compromise funds the next one. Trivy credentials enabled the npm CanisterWorm. npm tokens spread CanisterWorm to 66+ packages including telnyx. LiteLLM’s CI pipeline used the compromised Trivy, handing over PyPI publishing tokens. Checkmarx credentials came from environments that ran the compromised trivy-action. The cascade is by design.
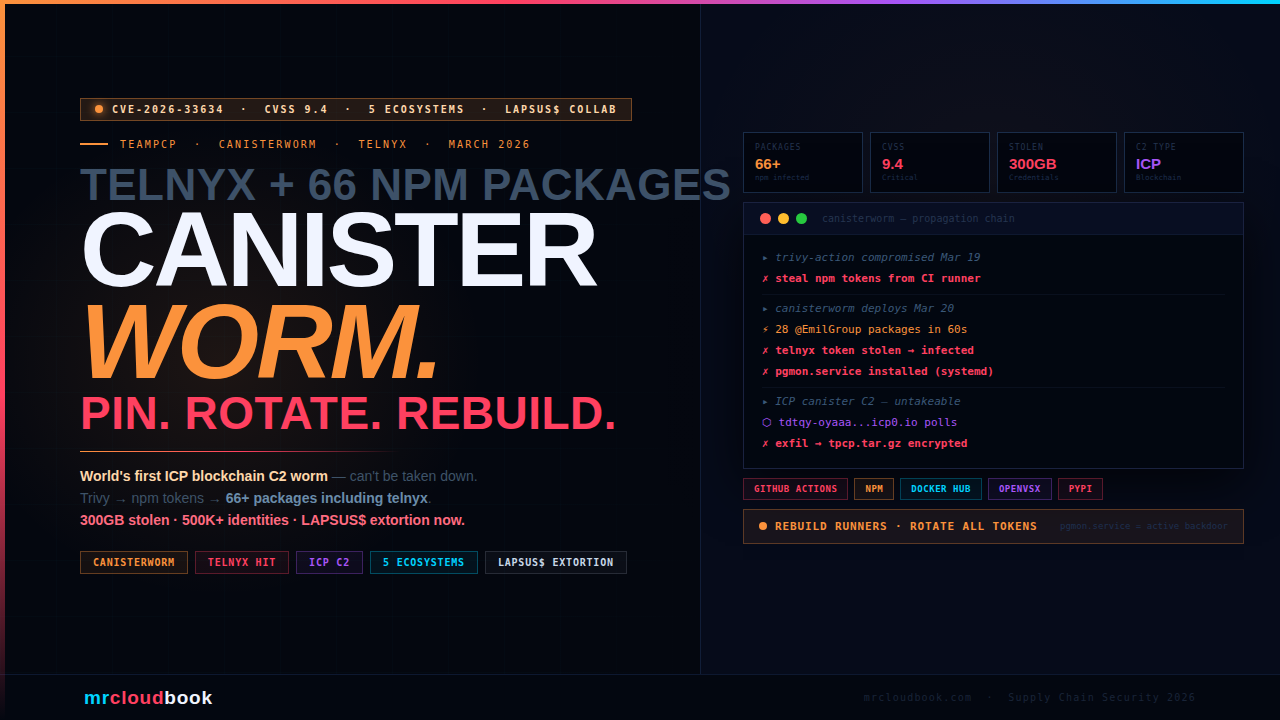
Now Collaborating with LAPSUS$ - Active Extortion Underway As of March 25, 2026, TeamPCP has pivoted from credential theft to active extortion. The FBI Assistant Director of Cyber Division confirmed TeamPCP is working through approximately 300 GB of compressed stolen credentials in collaboration with the LAPSUS$ extortion group. Mandiant estimates over 1,000 SaaS environments are already impacted, with projections of 5,000-10,000. If your organisation had a compromised environment during March 19-24, you may receive an extortion demand.
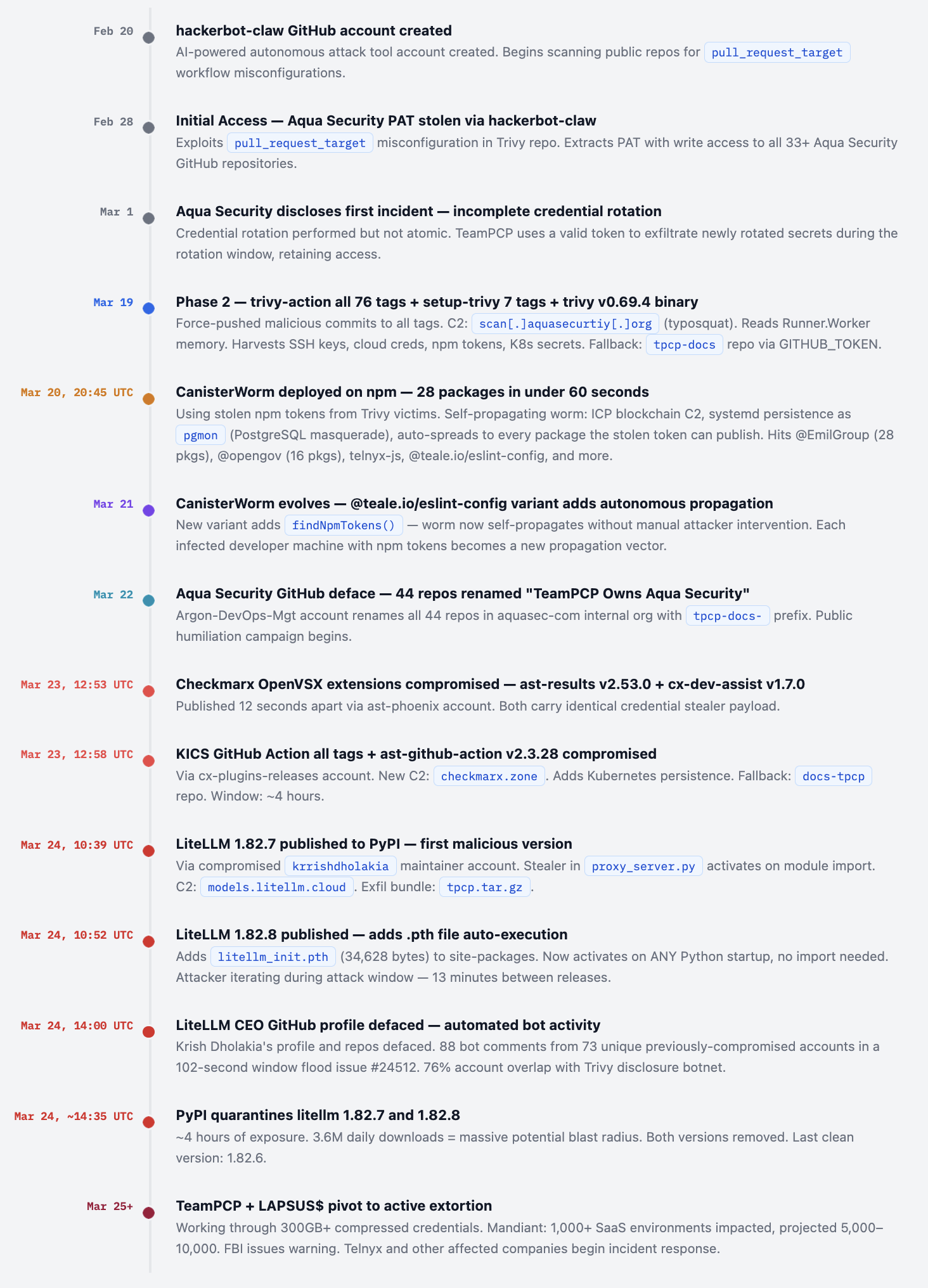
The Complete Attack Cascade - Feb 28 to Mar 27
This is not a single incident. It is a cascading, credential-powered campaign that used each victim’s secrets to compromise the next target. Every event in this timeline is connected.
CanisterWorm - The World’s First ICP-Powered npm Worm
CanisterWorm is not just another malicious npm package. It is the first self-propagating software worm in the npm ecosystem to use blockchain-based command and control - making it impossible to take down through conventional provider abuse reporting. Discovered by Aikido Security on March 20, 2026.
Three-Stage Architecture
01. Node.js postinstall hook - triggers on npm install
A malicious postinstall script in package.json activates automatically during installation. No user action required - just running npm install triggers the chain. Decodes a base64-encoded Python backdoor and writes it to ~/.local/share/pgmon/service.py.
02. Persistent Python backdoor - systemd service named pgmon
Installs a systemd user service called pgmon - disguised as PostgreSQL monitoring tooling. No root required. Restart=always with 5-second restart delay ensures it survives crashes. Starts immediately, persists across reboots. Uses paths like /tmp/pglog and /tmp/.pg_state to blend in.
03. ICP canister dead-drop C2 - cannot be taken down
The backdoor polls an Internet Computer Protocol (ICP) canister - a tamperproof smart contract on a decentralised blockchain. No single host, no single registrar, no takedown path. TeamPCP can push new payloads to all infected machines at any time by updating the canister, without republishing any package. Canister endpoint: tdtqy-oyaaa-aaaae-af2dq-cai.raw.icp0.io
04. Self-propagation - deploy.js spreads to every package the stolen token can publish
Scans for npm tokens in ~/.npmrc, environment variables, and live npm config. Calls npm /-/whoami to identify the account. Enumerates every publishable package. Bumps patch versions. Preserves original READMEs to avoid detection. Republishes malicious payload across entire scope - 28 packages in under 60 seconds in the @EmilGroup case.
The Kubernetes Kamikaze Wiper
The same ICP canister used for npm C2 also served a Kubernetes-focused payload. When deployed to clusters, it detects the system timezone and locale. On clusters configured for Iran (Tehran timezone or Farsi language), it deploys a DaemonSet wiper named kamikaze that mounts the host root filesystem, erases top-level content, and forces a reboot - destroying the entire cluster including the control plane. In other regions, it deploys privileged DaemonSets for persistence and lateral movement via SSH and exposed Docker APIs.
⚠ The ICP C2 Changes Everything About Takedowns Every previous supply chain attack with a C2 server could be neutered by taking down the domain or hosting provider. TeamPCP's ICP canister has no such weakness. There is no registrar to contact, no hosting provider to call, no single point of failure. The C2 will remain operational for as long as the ICP blockchain exists. This is the first documented use of this technique in a supply chain campaign and represents a genuine escalation in adversarial infrastructure.
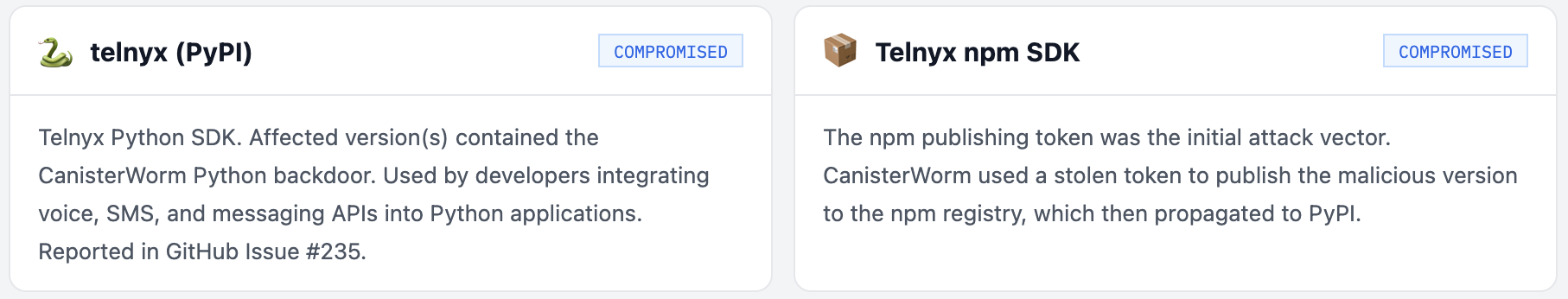
Telnyx - A CanisterWorm Victim
Telnyx, the cloud communications platform, had its PyPI package telnyx and npm SDK compromised as part of the CanisterWorm spread. The attack did not target Telnyx specifically - their npm publishing token was stolen from a developer or CI pipeline that had installed a CanisterWorm-infected package during the March 20 propagation wave.
This is the insidious mechanic of CanisterWorm: Telnyx was a downstream victim. Some developer or CI system at Telnyx (or at a company whose CI pipeline had access to Telnyx’s npm publishing scope) had previously installed one of the 66+ infected packages. When CanisterWorm ran, it found the Telnyx npm token in that environment and used it to publish a malicious version of the Telnyx package to npm and subsequently pushed it downstream to PyPI.
The GitHub issue team-telnyx/telnyx-python#235 was filed by a user who discovered the compromise and alerted the team. Telnyx responded by yanking the affected versions and rotating credentials.
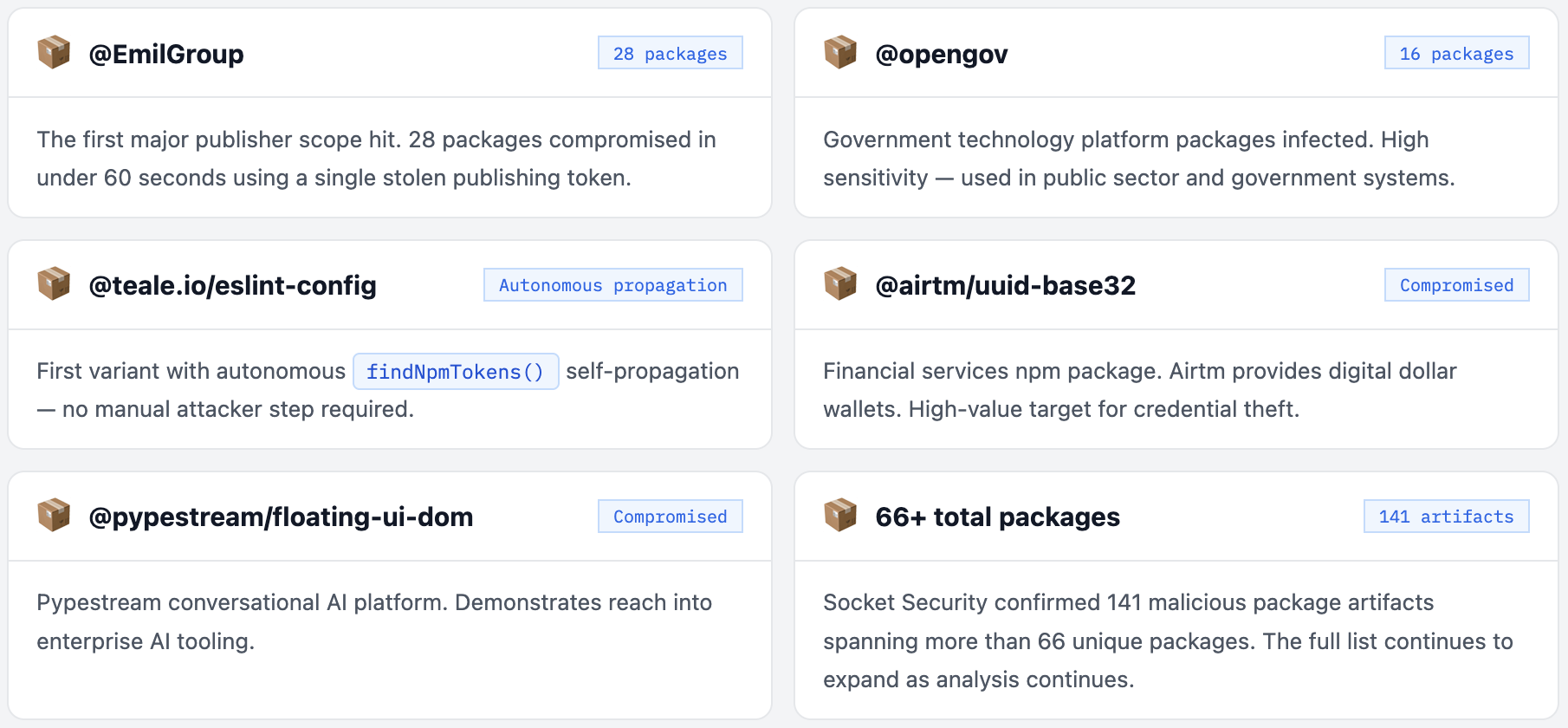
The Full List of CanisterWorm npm Victims
What the Malware Actually Does - Stage by Stage
The TeamPCP payload that hit every target in this campaign - Trivy, KICS, LiteLLM, telnyx, all 66+ npm packages - shares the same core credential stealer. The payload has evolved across the campaign with each iteration more capable than the last.
1. Cloud Provider Credentials
AWS: ~/.aws/credentials, environment vars AWS_ACCESS_KEY_ID, AWS_SECRET_ACCESS_KEY, EC2 IMDS tokens. GCP: service account JSON files, GOOGLE_APPLICATION_CREDENTIALS. Azure: service principal creds.
2. SSH Keys + Git Credentials
All private keys in ~/.ssh/. Git credentials from ~/.gitconfig and credential helpers. GitHub PATs from environment variables and CI/CD secrets.
3. Kubernetes Secrets
Kubeconfig files from ~/.kube/config. Service account tokens. Cluster API keys. Then deploys privileged DaemonSets to escape to every node in the cluster.
4. Developer Tokens - npm, PyPI, Docker
npm: ~/.npmrc, NPM_TOKEN env vars. PyPI: ~/.pypirc, TWINE_PASSWORD. Docker Hub: ~/.docker/config.json. These tokens seed the next propagation wave.
5. Cryptocurrency Wallets + .env Files
Wallet keystores, seed phrases from common paths. All .env files recursively from project directories. Database connection strings. API keys of all types.
6. Encryption + Exfiltration
Stolen data encrypted with AES-256-CBC + RSA-4096 using attacker’s embedded public key. Exfiltrated as tpcp.tar.gz to C2 (varies by target: models.litellm.cloud, checkmarx.zone, aquasecurtiy.org, ICP canister). Kill switch: aborts if C2 response contains youtube.
# 1. Check for pgmon systemd service (CanisterWorm persistence)
systemctl --user list-units | grep pgmon
ls -la ~/.config/systemd/user/pgmon.service 2>/dev/null && \
echo "INFECTED: pgmon backdoor found" || echo "pgmon not found"
# 2. Check for CanisterWorm files
ls -la ~/.local/share/pgmon/ 2>/dev/null
ls /tmp/pglog /tmp/.pg_state 2>/dev/null
# 3. Check for ICP canister connections in network logs
ss -tnp | grep "icp0.io\|tdtqy"
# 4. Check for malicious LiteLLM .pth file
find $(python3 -c "import site; print(':'.join(site.getsitepackages()))") \
-name "litellm_init.pth" 2>/dev/null && \
echo "INFECTED: litellm_init.pth found" || echo "litellm_init.pth not found"
# 5. Check telnyx package version
pip show telnyx 2>/dev/null | grep Version
npm list telnyx 2>/dev/null | grep telnyx
# 6. Audit all npm packages installed during March 19-24 window
# Check package-lock.json for suspicious patch version bumps
git log --after="2026-03-19" --before="2026-03-25" -- package-lock.json
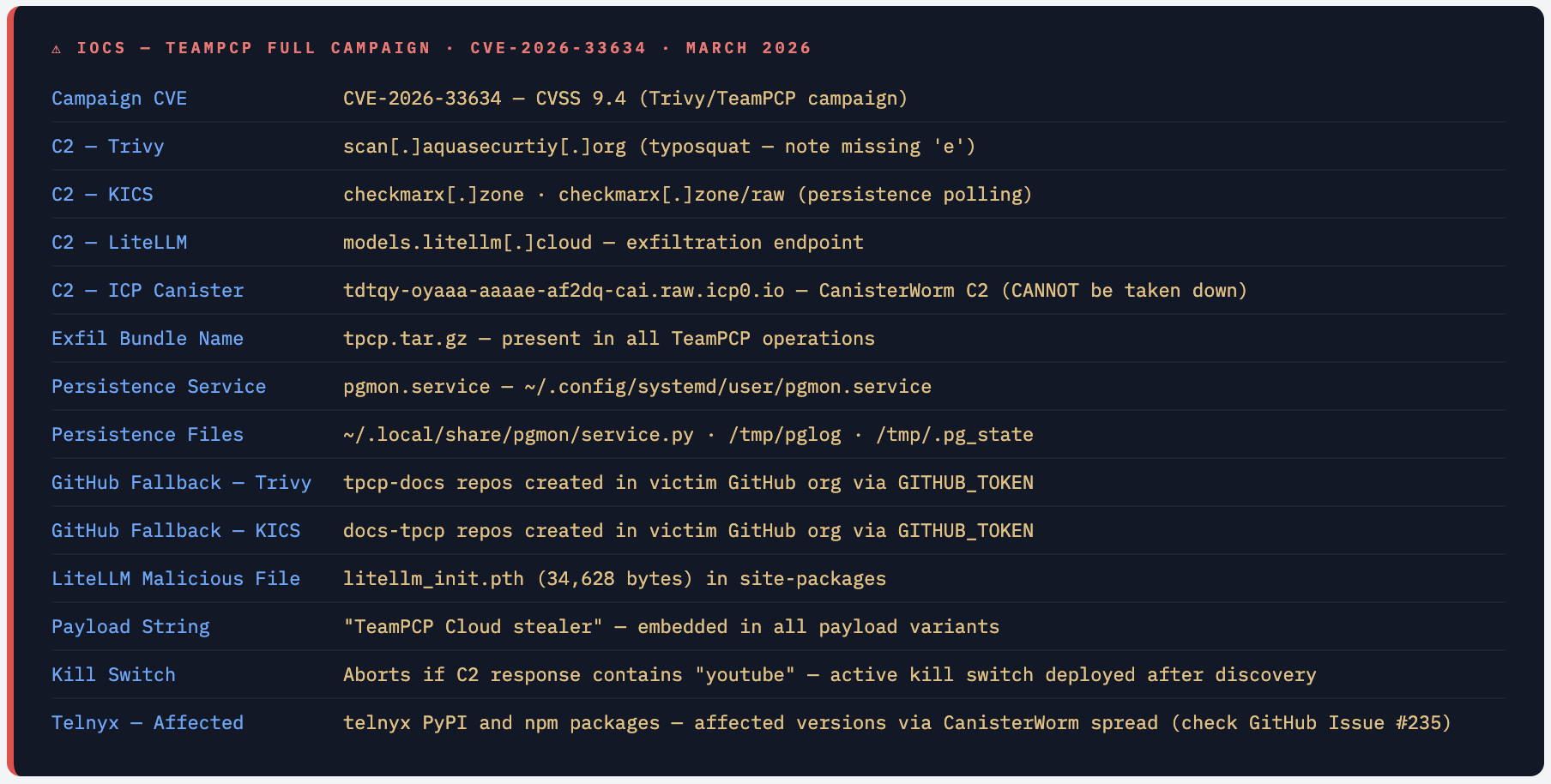
IOCs - Complete TeamPCP Campaign
Are You Affected? Complete Scope

If Your CI Used Trivy Between Mar 19-24 - You Are the Root Cause Vector Many organisations don't realise that installing a compromised package is just Phase 1. The real risk is what happened next in that CI environment: every token, key, and secret accessible to that pipeline was exfiltrated. That includes your npm publish token (seeding CanisterWorm), your PyPI token, your Docker Hub credentials, your AWS/GCP/Azure keys, and your Kubernetes config. If any of those tokens have write access to packages - you may be an unwitting CanisterWorm propagation vector right now.
What to Do Right Now
- Run the detection script above. Check for
pgmon.service,litellm_init.pth, and all CanisterWorm file indicators immediately. - Rotate everything if you ran any affected tooling during March 19-24:
npm tokens, PyPI tokens, Docker Hub tokens, AWS keys, GCP service accounts, Azure credentials, Kubernetes tokens, SSH keys, GitHub PATs. - If you use
telnyx: rotate all Telnyx API keys, check account activity for unexpected phone number activity, send payments, or API usage spikes. - Audit all npm packages in your lock files for unexpected patch version bumps between March 20-24. Any patch bump during that window from a publisher in the affected scopes is suspect.
- Kill and remove pgmon:
systemctl --user stop pgmon; systemctl --user disable pgmon; rm -f ~/.config/systemd/user/pgmon.service; rm -rf ~/.local/share/pgmon/ - Rebuild CI/CD runners from scratch. Do not simply rotate credentials on a potentially infected runner - the systemd backdoor survives credential rotation and will steal the new credentials.
- Pin all GitHub Actions to full commit SHAs. Tags can be force-pushed. SHAs cannot be changed. This is the single most effective prevention for the entire GitHub Actions attack class.
- Pin Python and npm dependencies with hashes.
pip install --require-hashes -r requirements.txt. Any tampered package with a different hash fails to install. - If you have npm publishing tokens in any CI environment, scope them to the minimum required packages. A token that can publish to 28 packages is 28x the blast radius of a token that can publish to one.
Detecting TeamPCP / CanisterWorm Activity
- rule: TeamPCP C2 Connection - All Known Domains
condition: |
evt.type = connect and fd.typechar = 4
and fd.sip.name in (
"scan.aquasecurtiy.org",
"checkmarx.zone",
"models.litellm.cloud"
)
priority: CRITICAL
tags: [TeamPCP, supply_chain, CVE-2026-33634]
- rule: CanisterWorm ICP Canister Polling
condition: |
evt.type = connect and fd.typechar = 4
and fd.sip.name contains "icp0.io"
priority: CRITICAL
tags: [CanisterWorm, TeamPCP, supply_chain]
- rule: pgmon Systemd Backdoor Installed
condition: |
evt.type in (open, openat) and
fd.name contains "pgmon.service"
priority: CRITICAL
tags: [CanisterWorm, persistence, TeamPCP]
- rule: tpcp.tar.gz Exfiltration
condition: |
(evt.type in (open, openat, write)) and
fd.name contains "tpcp.tar.gz"
priority: CRITICAL
tags: [TeamPCP, exfiltration]
- rule: Kubernetes DaemonSet Wiper Deployment
desc: TeamPCP kamikaze wiper - targets Iran-configured clusters
condition: |
ka.verb = create and
ka.target.resource = daemonsets and
not ka.user.name in (trusted_daemonset_operators)
priority: CRITICAL
tags: [CanisterWorm, kubernetes, destructive]
What This Campaign Changes
The TeamPCP March 2026 campaign is a watershed moment for software supply chain security. Not because it introduced a new vulnerability class - every individual technique (tag-hijacking, PyPI credential abuse, npm worms, Kubernetes persistence) was known. It is a watershed because TeamPCP assembled all of these into a self-funding, self-propagating cascade that crossed five ecosystems in five days, generated a novel ICP-powered worm that cannot be taken down, and compromised tools specifically chosen because they run with elevated trust in security-sensitive environments.
The most chilling detail: the most security-conscious organisations had the greatest exposure. If you ran Trivy on every build, you were more exposed than someone who skipped it. If you ran KICS on every infrastructure change, your IaC secrets were stolen. The tools you deployed to improve your security posture became the primary attack surface.
Telnyx is one of dozens of collateral victims - organisations whose npm tokens were present in an environment that installed a compromised package. They did nothing wrong. Their token was in a CI environment that installed one of 66+ infected packages. The worm found it, used it, and published malicious code under their name before they knew anything had happened.
Pin Everything. Rotate Everything. Rebuild Your Runners.
SHA pinning, hash-locked dependencies, scoped publishing tokens, and runtime egress monitoring would have stopped this campaign at every stage. These are not novel controls - they have been best practice for years. This campaign is the proof of what happens when they remain advisory.

Comments (0)
No comments yet. Be the first to share your thoughts.
Leave a comment