Trivy Got Hacked: What Actually Happened
Source: GitHub Discussion #10265
Announced: March 1, 2026
Project: aquasecurity/trivy - vulnerability/misconfiguration scanner for containers and other artifacts
Executive Summary
Trivy was compromised through a GitHub Actions workflow vulnerability, part of a broader campaign (HackerBot-Claw) targeting multiple projects. An attacker obtained a Personal Access Token (PAT) with broad permissions, then used it to rename the repository, delete releases, and publish a malicious VSCode extension. Source code was not modified; container images and package-manager installs were not tampered with. Direct downloads from GitHub and related tooling were temporarily broken. The maintainers fixed the workflow, republished the latest release, and enabled immutable releases.
1. Root Cause
1.1 Vulnerability
- Vector: A GitHub Actions workflow using
on: pull_request_target. - Mechanism: With
pull_request_target, the workflow runs in the context of the base repository (including its secrets), while using the code from the pull request. A malicious PR can therefore trigger workflows that have access to repository secrets and exfiltrate or misuse them. - Reference: StepSecurity - HackerBot Claw GitHub Actions Exploitation.
- Fix: The vulnerable workflow was removed/updated in PR #10259.
1.2 Attack Chain (Timeline)
| Time (UTC) | Event |
|---|---|
| Feb 27, 00:18 | PR #10252 created and immediately closed, triggering CI and exposing secrets. PR and user were later deleted (e.g. by GitHub as bot/spam). |
| Feb 27, 12:01 | Unauthorized API activity begins using the compromised PAT. |
| Feb 27, 12:36 | Malicious security advisory created in the trivy-vscode-extension repository. |
| Feb 28, 03:17 | hackerbot-claw PR created and closed (same pattern: trigger CI to abuse workflow). |
| Mar 1, 00:14 | Mass deletion of releases (e.g. via script). |
| Mar 1, 00:27 | Repository renamed to private-trivy; fake/empty repository put in place of the public Trivy repo. |
The maintainers assessed that the same attacker was behind PR #10252 and the hackerbot-claw activity (e.g. country code, user agent, same PAT hash, behavioral pattern of “open + close PR to trigger CI”).
2. Impact
2.1 Confirmed Impact
| Area | Description |
|---|---|
| Repository | Made private and renamed to https://github.com/aquasecurity/private-trivy. An empty repo was published as the public Trivy repository. |
| Releases | GitHub Releases from v0.27.0 through v0.69.1 were deleted, including associated GitHub Discussions and release assets. |
| VSCode extension | A malicious artifact was built and published to the Open VSIX marketplace (alternative to the official VS Code marketplace). The artifact was removed and the publish token revoked. |
| Stars & forks | When the public repo was effectively replaced/deleted, stars were lost. Forks were re-parented; e.g. fossabot/trivy gained a large number of forks. GitHub does not automatically restore stars; recovery may require GitHub Support. |
2.2 What Was Not Compromised (Per Maintainers)
- Source code: No malicious code was added. Integrity can be checked via commit IDs.
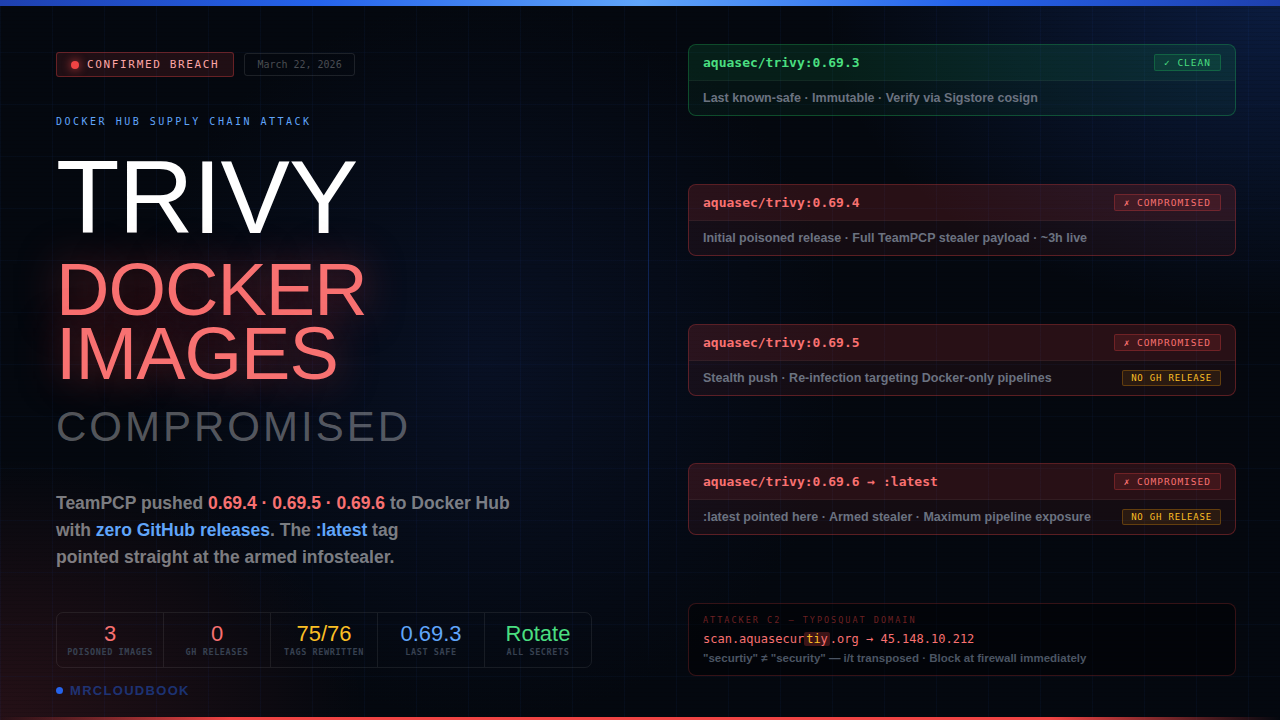
- Container image (Docker): No observed compromise; usage via container image is considered safe.
- Package managers: No observed compromise; usage via package managers is considered safe.
- trivy-db: Database and vuln-list-update were restored; trivy-db is safe to use.
- get.trivy.dev: Deployments were reviewed (e.g. since December); only legitimate pipeline-triggered deployments were found, with deployment IDs matching pipeline logs.
2.3 What Was Temporarily Broken
- Direct binary download from GitHub (release assets were deleted).
- get.trivy.dev and the install script (they depend on release assets).
- Trivy GitHub Action (e.g.
aquasecurity/trivy-action@0.34.1defaulting to v0.69.1 failed until users could point to a republished version).
3. Verification & Integrity
3.1 Container Image Signing (Cosign)
- v0.69.2 was republished quickly; its keyless signature still referred to the renamed repo (
private-trivy), so Cosign verification failed with a SAN mismatch: - Expected:
^https://github.com/aquasecurity/trivy/.* - Got:
https://github.com/aquasecurity/private-trivy/.github/workflows/reusable-release.yaml@refs/tags/v0.69.2 - v0.69.3 was built and signed after the repo was restored; its signature contains the correct repository and is the recommended tag for signature verification.
3.2 Deleted Release Assets
- Previous release assets (0.27.0-0.69.1) could not be re-checked after deletion; they are gone from GitHub.
- The install script and get.trivy.dev historically served these assets; any past downloads from those releases cannot be re-verified from GitHub.
- Community extraction of expected hashes (e.g. gist) may help only if you have another source of the same binaries to compare.
3.3 Vulnerable Workflow History
- The workflow using
pull_request_targethad been present since at least October 7, 2025. - Full impact over that window (e.g. which releases or artifacts could have been modified) has been discussed; maintainers have not identified impact beyond what is described in the discussion.
4. Response & Mitigation
4.1 Immediate
- Vulnerable workflow removed/updated (PR #10259).
- Malicious VSCode artifact removed from Open VSIX; publish token revoked.
- Latest version republished as v0.69.2 so downloads and automation could resume.
- v0.69.3 released with immutable releases enabled and correct container signature.
4.2 Hardening
- Immutable releases enabled on the main Trivy repo (from v0.69.3).
- Immutable releases enabled on trivy-action as well.
- trivy-db vuln-list-update and related functionality restored.
4.3 Recovery Still Pending / Limited
- Older releases (0.27.0-0.69.1): Maintainers are looking into ways to re-publish; not all may be restored.
- Stars: Not restored by GitHub automatically; Trivy team contacted GitHub Support (recovery possible in some cases, e.g. Elastic’s incident).
- Fork network: May need GitHub Support to re-parent forks under the restored repository.
5. Recommendations for Users
5.1 If You Use Trivy
| Usage | Action |
|---|---|
| Container image | Prefer v0.69.3 (or later) and verify with Cosign; v0.69.2 signature will show wrong SAN. |
| Binary from GitHub / install script / get.trivy.dev | Use v0.69.2 or v0.69.3 (or newer); avoid relying on deleted releases. |
| Trivy Action | Pin a known-good version, e.g. version: 'v0.69.3' (or newer), and follow trivy-action for immutable release tags. |
| VSCode extension | Install only from the official VS Code marketplace, not from Open VSIX, and ensure you did not install the malicious build during the incident window. |
| trivy-db | Safe to use; no impact identified. |
5.2 If You Maintain Projects Using GitHub Actions
- Audit workflows that use
pull_request_targetand ensure they do not expose secrets to untrusted PR code. - Prefer least-privilege tokens and fine-grained PATs; avoid broad-scope tokens for release or publish steps.
- Consider environment protection rules and required reviewers for deployment/release workflows.
- Consider immutable releases where supported (e.g. GitHub, Docker Hub) to limit deletion or overwrite of published artifacts.
- Use tooling (e.g. zizmor) to scan for GitHub Actions misconfigurations.
6. References
- Incident discussion: Trivy security incident 2026-03-01 - Discussion #10265
- Workflow fix: PR #10259
- HackerBot-Claw context: StepSecurity - HackerBot Claw GitHub Actions Exploitation
- trivy-action update (post-incident): aquasecurity/trivy-action#513
- Misconfiguration scanning idea for Trivy: Discussion #10278
- Expected hashes (community): klassiker’s gist - verify independently before use.
- Aqua Security (org) contact: github.com/aquasecurity (e.g. for security contact).
7. Summary Table
| Item | Status |
|---|---|
| Cause | GitHub Actions pull_request_target workflow; PAT exfiltrated and abused. |
| Codebase | Not modified (commit integrity intact). |
| Releases 0.27.0-0.69.1 | Deleted; assets not re-verifiable on GitHub. |
| Container image | Not compromised; use v0.69.3+ and verify with Cosign. |
| trivy-db | Restored; safe to use. |
| VSCode extension | Malicious build removed; use only official marketplace. |
| Current recommended version | v0.69.3 (or later) with immutable releases and correct signing. |
Created from the official Trivy security incident discussion (2026-03-01). For the latest updates, refer to Discussion #10265.


Comments (0)
No comments yet. Be the first to share your thoughts.
Leave a comment